Sicherung industrieller Netzwerke gegenüber IT-Netzwerken
Previously we looked at the question of 'Why are PLCs so insecure?' Today we are going to come at SCADA security from another angle, which is 'Why is securing Industrial Networks different than securing IT Networks?' We will also look at three ways to address these differences.
Recently Belden hosted an Industrial Ethernet Infrastructure Design Seminar including a session by Mark Cooksley, Hirschmann* network management product manager called Introduction to Network Security. Mark did a great job of explaining why Industrial Control Systems (ICS) are easy cyber targets and also shared high-level solutions for securing them.
Industrial Control Systems are not IT Systems
Sound familiar?
'None of this would be a problem if those plant floor people just used proper security policies—what’s wrong with them?'
- IT Manager after a security incident

The heart of IT network systems is often a secure, climate-controlled data center where equipment is usually standardized and less than 10 years old. In contrast, The heart of industrial control network systems is on the plant floor, often in a hazardous environment with an average equipment life of more than 10 years.
Herein lies the misunderstanding between IT and ICS networks. Now, while you might be fully aware of what they are, I will call them out in case you need a handy list for a future chat with an IT professional.
Differences between IT & ICS Network Security Requirements
- Performance requirements
- Reliability requirements
- Operating systems & applications
- Risk management goals
- Security architectures
- Security goals
- Differing assumptions about security, often incompatible ones
Protect the Data vs Protect the Process
The primary goal of IT security is rooted in the privacy concerns whereas the number one goal of ICS security is based on process security concerns. Differences in the top three priorities are summarized below:
Priority |
IT |
SCADA/ICS |
|---|---|---|
| 1. |
Vertraulichkeit |
Verfügbarkeit |
| 2. | Integrität | Integrität |
| 3. |
Verfügbarkeit |
Vertraulichkeit |
Security Issues in Control Networks
Most ICS system security issues fall into three main categories:
1. Soft Targets: Control networks are full of what are called 'soft' targets—devices that are extremely vulnerable to disruption through their network interface. PCs in many plants run for weeks or months without any security updates, and some even operate without any anti-virus tools. In addition, many of the controllers in these networks were designed in an era when cyber security was not a concern; as a result, many of these devices can be disrupted by malformed network traffic or even by high volumes of correctly-formed traffic.
2. Multiple Pathways: Many control networks have multiple pathways through which cybersecurity threats can enter the plant. These pathways often bypass existing security measures and some aren't captured on a network diagram. Consider laptop computers carried in and out of facilities or USB keys that move from one PC to another. These can easily bring malware into the plant and rapidly spread it from one system to another.
3. 'Flat' Networks: Unfortunately many ICS networks are implemented as large 'flat' networks with no isolation between unrelated sub-systems. Should a problem occur in one part of the plant, it can spread very quickly to other sub-systems and remote sites.
Security Solutions
Mark presented 3 high level approaches to securing SCADA and ICS systems.
Harden the Perimeter
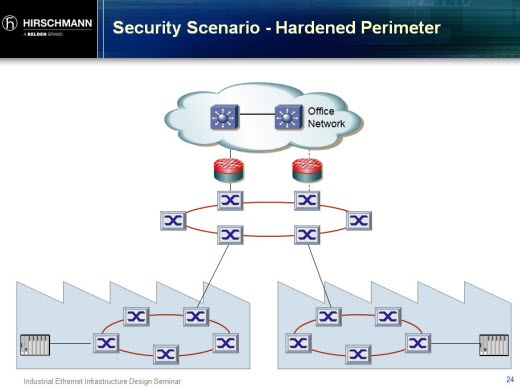
The idea of isolating the plant network from the office network with firewalls and a DMZ is considered common sense and is therefore a measure that you should easily align on with IT colleagues. (See Hirschmann firewalls designed for this purpose.
Defense in Depth
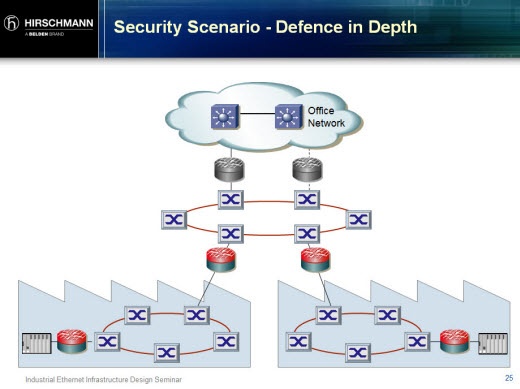
The concept of Defense in Depth (DID) goes beyond the security perimeter with layers of defense throughout the control network. With a layered approach, should malware or inappropriate network traffic breach the perimeter, it can be stopped and/or contained by defenses at other points in the system. For example, removable media used in the plant could introduce malware. The Tofino industrially hardened security solution is uniquely designed for this purpose—it's easily configured and installed on live plant networks without plant downtime and secures industrial protocols.
An IT analogy for industrial DID is the antivirus (AV) and personal firewall software installed on PCs. There are many reasons industrial control devices such as PLCs and DCS aren't running security software-including the lack of such security software available for PLCs. Unfortunately, this doesn't mean there's an equal lack of security threats for PLCs making industrial firewalls a solid option for securing these devices.
Remote-Zugriff
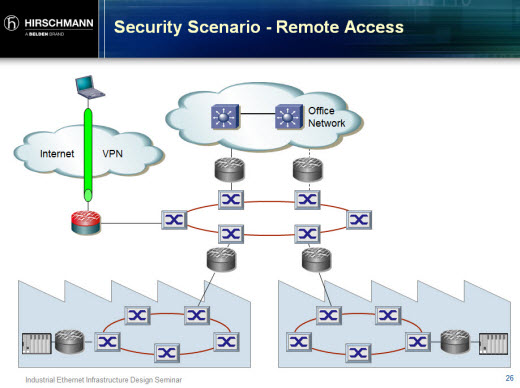
Another way malware or inappropriate network traffic could penetrate the perimeter firewall is through remote access for maintenance or other application needs. To secure this type of connectivity, VPNs are recommended—a method commonly deployed by IT professionals.
Additional Recommendations
To further address the challenge of securing control networks, we recommend:
- Following best practices outlined in the joint White Paper with exida '7 Steps to ICS & SCADA Security'
- Learning & applying ISA IEC 62443 standards**
- Focusing security efforts on the 'crown jewels' of your operation
Cybersecurity Inertia is Still Common
During he session, Mark shared many occasions when he'd been called to client sites to retroactively assist with network security. Too often, companies take a passive approach. Unfortunately the reality is not if but when a cyberattack will occur. It's important to get started and resist the idea that plant cybersecurity is overly complex or costly. The session was aptly closed with this Japanese proverb, 'When you are thirsty, it is too late to think about digging a well".
* Hirschmann is a Belden brand.
** Formerly ANSI/ISA-99 Standards.
© Tofino Security 2012 | All Rights Reserved | Tofino Security is a Belden Brand
